

防火墙双机组网环境中的IPSecVPN实验步骤及配置
描述
实验拓扑
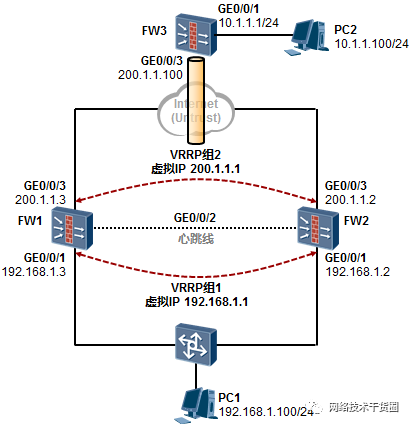
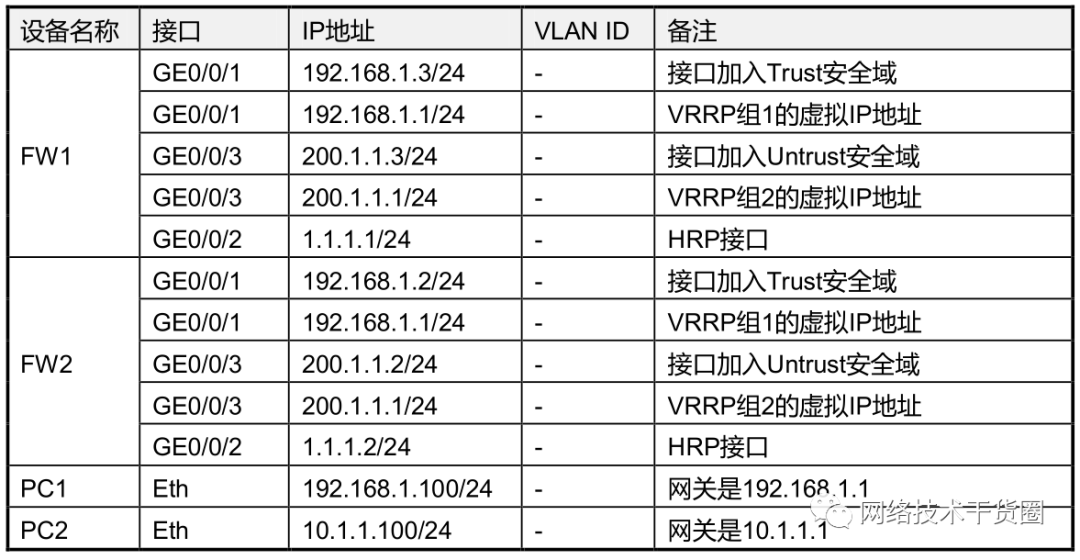
网络中各设备的IP地址规划及接口描述如下:
实验需求
设备IP、VLAN规划如上表所示;
FW1/FW2部署双机热备,采用主备方式,FW1为主设备,FW2为备设备;
PC1是站点内网用户,处于Trust Zone网关是主备防火墙的VRRP组1的虚拟IP地址;
PC2是另一个站点的内网用户,处于Untrust Zone,网关设置为FW3的GE0/0/1口IP地址;
FW1/FW2与FW3之间建立一条IPSecVPN站点到站点的隧道,用于保护PC1及PC2之间的互访流量。
实验步骤及配置
完成接口的基本配置,将接口关联到安全区域
FW1的配置如下:
[FW1] interface GigabitEthernet 0/0/1 [FW1-GigabitEthernet0/0/1] ip address 192.168.1.3 24 [FW1-GigabitEthernet0/0/1] vrrp vrid 1 virtual-ip 192.168.1.1 master [FW1-GigabitEthernet0/0/1] quit [FW1] interface GigabitEthernet 0/0/3 [FW1-GigabitEthernet0/0/3] ip address 200.1.1.3 24 [FW1-GigabitEthernet0/0/3] vrrp vrid 2 virtual-ip 200.1.1.1 master [FW1-GigabitEthernet0/0/3] quit [FW1] interface GigabitEthernet 0/0/2 [FW1-GigabitEthernet0/0/2] ip address 1.1.1.1 24 [FW1-GigabitEthernet0/0/2] quit [FW1] firewall zone trust [FW1-zone-trust] add interface GigabitEthernet 0/0/1 [FW1-zone-trust] quit [FW1] firewall zone untrust [FW1-zone-untrust] add interface GigabitEthernet 0/0/3 [FW1-zone-untrust] quit [FW1] firewall zone name ha [FW1-zone-ha] set priority 96 [FW1-zone-ha] add interface GigabitEthernet 0/0/2 [FW1-zone-ha] quit
FW2的配置如下:
[FW2] interface GigabitEthernet 0/0/1 [FW2-GigabitEthernet0/0/1] ip address 192.168.1.2 24 [FW2-GigabitEthernet0/0/1] vrrp vrid 1 virtual-ip 192.168.1.1 slave [FW2-GigabitEthernet0/0/1] quit [FW2] interface GigabitEthernet 0/0/3 [FW2-GigabitEthernet0/0/3] ip address 200.1.1.2 24 [FW2-GigabitEthernet0/0/3] vrrp vrid 2 virtual-ip 200.1.1.1 slave [FW2-GigabitEthernet0/0/3] quit [FW2] interface GigabitEthernet 0/0/2 [FW2-GigabitEthernet0/0/2] ip address 1.1.1.2 24 [FW2-GigabitEthernet0/0/2] quit [FW2] firewall zone trust [FW2-zone-trust] add interface GigabitEthernet 0/0/1 [FW2-zone-trust] quit [FW2] firewall zone untrust [FW2-zone-untrust] add interface GigabitEthernet 0/0/3 [FW2-zone-untrust] quit [FW2] firewall zone name ha [FW2-zone-ha] set priority 96 [FW2-zone-ha] add interface GigabitEthernet 0/0/2 [FW2-zone-ha] quit
为FW1及FW2添加默认路由
FW1的配置如下:
[FW1] ip route-static 0.0.0.0 0 200.1.1.100
FW2的配置如下:
[FW2] ip route-static 0.0.0.0 0 200.1.1.100
部署FW1/FW2双机热备,采用主备方式
FW1的配置如下:
[FW1] hrp interface GigabitEthernet 0/0/2 [FW1] hrp enable [FW1] hrp preempt delay 60
FW2的配置如下:
[FW2] hrp interface GigabitEthernet 0/0/2 [FW2] hrp enable
配置完成后,FW1/FW2会进行主备协商,FW1成为主防火墙,FW2成为备份防火墙。
在FW1及FW2上配置IPSecVPN
IPSecVPN相关策略的配置在主防火墙FW1上配置即可,这些配置会自动同步到备份防火墙FW2上,不过,在接口上应用IPSec Policy的这一条命令,是需要在主备防火墙相应的接口上都做配置的,因为这条命令不会自动同步。
在主防火墙FW1上定义IPSecVPN感兴趣数据流,使用ACL3000来匹配感兴趣流量:
HRP_M [FW1] acl number 3000 HRP_M [FW1-acl-adv-3000] rule permit ip source 192.168.1.0 0.0.0.255 destination 10.1.1.0 0.0.0.255 HRP_M [FW1-acl-adv-3000] quit
在主防火墙FW1上配置IKE Proposal,这是IKE阶段一的策略,在FW1/FW2上部署的相关策略均需与FW3相匹配。IKE阶段一的策略中,身份验证使用的是预共享的认证方式,验证算法使用的是sha1,加密算法使用3des:
HRP_M [FW1] ike proposal 10 HRP_M [FW1-ike-proposal-10] authentication-method pre-share HRP_M [FW1-ike-proposal-10] authentication-algorithm sha1 HRP_M [FW1-ike-proposal-10] encryption-algorithm 3des-cbc HRP_M [FW1-ike-proposal-10] dh group2 HRP_M [FW1-ike-proposal-10] quit
在主防火墙FW1上配置IPsec proposal,这是IKE阶段二的策略,在阶段二的策略中安全协议采用ESP,加密算法使用3des,验证算法使用sha1:
HRP_M [FW1] ipsec proposal myset HRP_M [FW1-ipsec-proposal-myset] transform esp HRP_M [FW1-ipsec-proposal-myset] esp authentication-algorithm sha1 HRP_M [FW1-ipsec-proposal-myset] esp encryption-algorithm 3des
在主防火墙FW1上配置IKE peer,定义预共享秘钥、关联IKE proposal并指定隧道对端节点IP
HRP_M [FW1] ike peer fw3 HRP_M [FW1-ike-peer-fw3] pre-shared-key Huawei123 HRP_M [FW1-ike-peer-fw3] ike-proposal 10 HRP_M [FW1-ike-peer-fw3] remote-address 200.1.1.100
在主防火墙FW1上配置IPsec Policy
HRP_M [FW1] ipsec policy mymap 10 isakmp HRP_M [FW1-ipsec-policy-isakmp-mymap-10] security acl 3000 HRP_M [FW1-ipsec-policy-isakmp-mymap-10] ike-peer fw3 HRP_M [FW1-ipsec-policy-isakmp-mymap-10] local-address 200.1.1.1 HRP_M [FW1-ipsec-policy-isakmp-mymap-10] proposal myset
上述关于IPSecVPN的策略都能够自动同步到备机FW2上,但是下面这条将IPsec Policy 应用到接口的命令,需要在FW2上手工输入:
FW1应用IPsec Policy到接口
HRP_M [FW1] interface GigabitEthernet0/0/3 HRP_M [FW1-GigabitEthernet0/0/3] ipsec policy mymap
FW2应用IPsec Policy到接口
HRP_S [FW2] interface GigabitEthernet0/0/3 HRP_S [FW2-GigabitEthernet0/0/3] ipsec policy mymap
在FW1、FW2上放开防火墙之间的IPSecVPN隧道协商流量、放开IPSecVPN内部站点之间的流量
放开FW1、FW2防火墙自身到的FW3的流量,使得ISAKMP报文,以及受保护的用户数据能够发送到FW3
HRP_M[FW1] policy interzone local untrust outbound HRP_M[FW1-policy-interzone-local-untrust-outbound] policy 0 HRP_M[FW1-policy-interzone-local-untrust-outbound-0] policy destination 200.1.1.100 0 HRP_M[FW1-policy-interzone-local-untrust-outbound-0] action permit HRP_M[FW1-policy-interzone-local-untrust-outbound-0] quit HRP_M[FW1-policy-interzone-local-untrust-outbound] quit
放开IPSecVPN隧道对端防火墙发送到FW1/FW2的流量
HRP_M [FW1] policy interzone local untrust inbound HRP_M [FW1-policy-interzone-local-untrust-inbound] policy 0 HRP_M [FW1-policy-interzone-local-untrust-inbound-0] policy source 200.1.1.100 0 HRP_M [FW1-policy-interzone-local-untrust-inbound-0] action permit
放开对端站点内网访问本地内网的流量
HRP_M [FW1] policy interzone trust untrust inbound HRP_M [FW1-policy-interzone-trust-untrust-inbound] policy 0 HRP_M [FW1-policy-interzone-trust-untrust-inbound-0] policy source 10.1.1.0 0.0.0.255 HRP_M [FW1-policy-interzone-trust-untrust-inbound-0] policy destination 192.168.1.0 0.0.0.255 HRP_M [FW1-policy-interzone-trust-untrust-inbound-0] action permit
放开本地站点内网到对端站点内网的流量
HRP_M [FW1] policy interzone trust untrust outbound HRP_M [FW1-policy-interzone-trust-untrust-outbound] policy 0 HRP_M [FW1-policy-interzone-trust-untrust-outbound-0] policy source 192.168.1.0 0.0.0.255 HRP_M [FW1-policy-interzone-trust-untrust-outbound-0] policy destination 10.1.1.0 0.0.0.255 HRP_M [FW1-policy-interzone-trust-untrust-outbound-0] action permit
完成FW3的配置
[FW3] interface GigabitEthernet 0/0/1 [FW3-GigabitEthernet0/0/1] ip address 10.1.1.1 24 [FW3-GigabitEthernet0/0/1] quit [FW3] interface GigabitEthernet 0/0/3 [FW3-GigabitEthernet0/0/3] ip address 200.1.1.100 24 [FW3-GigabitEthernet0/0/3] quit [FW3] firewall zone trust [FW3-zone-trust] add interface GigabitEthernet 0/0/1 [FW3-zone-trust] quit [FW3] firewall zone untrust [FW3-zone-untrust] add interface GigabitEthernet 0/0/3 [FW3-zone-untrust] quit [FW3] acl number 3000 [FW3-acl-adv-3000] rule permit ip source 10.1.1.0 0.0.0.255 destination 192.168.1.0 0.0.0.255 [FW3-acl-adv-3000] quit [FW3] ike proposal 10 [FW3-ike-proposal-10] authentication-method pre-share [FW3-ike-proposal-10] authentication-algorithm sha1 [FW3-ike-proposal-10] encryption-algorithm 3des-cbc [FW3-ike-proposal-10] dh group2 [FW3-ike-proposal-10] quit [FW3] ipsec proposal myset [FW3-ipsec-proposal-myset] transform esp [FW3-ipsec-proposal-myset] esp authentication-algorithm sha1 [FW3-ipsec-proposal-myset] esp encryption-algorithm 3des [FW3] ike peer fw1-2 [FW3-ike-peer-fw1-2] pre-shared-key Huawei123 [FW3-ike-peer-fw1-2] ike-proposal 10 [FW3-ike-peer-fw1-2] remote-address 200.1.1.1 [FW3] ipsec policy mymap 10 isakmp [FW3-ipsec-policy-isakmp-mymap-10] security acl 3000 [FW3-ipsec-policy-isakmp-mymap-10] ike-peer fw1-2 [FW3-ipsec-policy-isakmp-mymap-10] proposal myset [FW3] interface GigabitEthernet0/0/3 [FW3-GigabitEthernet0/0/3] ipsec policy mymap [FW3] policy interzone local untrust outbound [FW3-policy-interzone-local-untrust-outbound] policy 0 [FW3-policy-interzone-local-untrust-outbound-0] policy destination 200.1.1.1 0 [FW3-policy-interzone-local-untrust-outbound-0] action permit [FW3-policy-interzone-local-untrust-outbound-0] quit [FW3-policy-interzone-local-untrust-outbound] quit
放开IPSecVPN隧道对端防火墙发送过来的流量
[FW3] policy interzone local untrust inbound [FW3-policy-interzone-local-untrust-inbound] policy 0 [FW3-policy-interzone-local-untrust-inbound-0] policy source 200.1.1.1 0 [FW3-policy-interzone-local-untrust-inbound-0] action permit
放开对端站点内网过来的流量
[FW3] policy interzone trust untrust inbound [FW3-policy-interzone-trust-untrust-inbound] policy 0 [FW3-policy-interzone-trust-untrust-inbound-0] policy source 192.168.1.0 0.0.0.255 [FW3-policy-interzone-trust-untrust-inbound-0] policy destination 10.1.1.0 0.0.0.255 [FW3- policy-interzone-trust-untrust-inbound-0] action permit
放开本地站点内网到对端站点内网的流量
[FW3] policy interzone trust untrust outbound [FW3-policy-interzone-trust-untrust-outbound] policy 0 [FW3-policy-interzone-trust-untrust-outbound-0] policy source 10.1.1.0 0.0.0.255 [FW3-policy-interzone-trust-untrust-outbound-0] policy destination 192.168.1.0 0.0.0.255 [FW3- policy-interzone-trust-untrust-outbound-0] action permit [FW3] ip route-static 0.0.0.0 0 200.1.1.1
完成上述配置后,PC1与PC2即可互访。
HRP_M[FW1] display ipsec sa =============================== Interface: GigabitEthernet0/0/8 path MTU: 1500 =============================== ----------------------------- IPsec policy name: "mymap" sequence number: 10 mode: isakmp vpn: public ----------------------------- connection id: 40002 rule number: 5 encapsulation mode: tunnel holding time: 49710d 5h 29m 28s tunnel local : 200.1.1.1 tunnel remote: 200.1.1.100 flow source: 192.168.1.0/255.255.255.0 0/0 flow destination: 10.1.1.0/255.255.255.0 0/0 [inbound ESP SAs] spi: 3990067008 (0xedd39740) vpn: public said: 0 cpuid: 0x0000 proposal: ESP-ENCRYPT-3DES ESP-AUTH-SHA1 sa remaining key duration (bytes/sec): 1887436464/2704 max received sequence-number: 4 udp encapsulation used for nat traversal: N [outbound ESP SAs] spi: 1474676474 (0x57e5c6fa) vpn: public said: 1 cpuid: 0x0000 proposal: ESP-ENCRYPT-3DES ESP-AUTH-SHA1 sa remaining key duration (bytes/sec): 1887436464/2704 max sent sequence-number: 260004 udp encapsulation used for nat traversal: N
以上是FW1的IPSec SAs。主防火墙FW1在与FW3完成IPSecVPN隧道的建立后,会将IPSec SAs同步到备份防火墙上,备份防火墙上的IPSec SAs与主防火墙上的SAs是一样的:
HRP_S[FW2] display ipsec sa =============================== Interface: GigabitEthernet0/0/8 path MTU: 1500 =============================== ----------------------------- IPsec policy name: "mymap" sequence number: 10 mode: isakmp vpn: public ----------------------------- connection id: 40005 rule number: 5 encapsulation mode: tunnel holding time: 0d 0h 58m 19s tunnel local : 200.1.1.1 tunnel remote: 200.1.1.100 flow source: 192.168.1.0/255.255.255.0 0/0 flow destination: 10.1.1.0/255.255.255.0 0/0 [inbound ESP SAs] spi: 3990067008 (0xedd39740) vpn: public said: 4 cpuid: 0x0000 proposal: ESP-ENCRYPT-3DES ESP-AUTH-SHA1 sa remaining key duration (bytes/sec): 1887436464/2618 max received sequence-number: 1 udp encapsulation used for nat traversal: N [outbound ESP SAs] spi: 1474676474 (0x57e5c6fa) vpn: public said: 5 cpuid: 0x0000 proposal: ESP-ENCRYPT-3DES ESP-AUTH-SHA1 sa remaining key duration (bytes/sec): 1887436464/2618 max sent sequence-number: 520000 udp encapsulation used for nat traversal: N HRP_S[FW2]
当FW1丢失了到Internet的连接,如下:
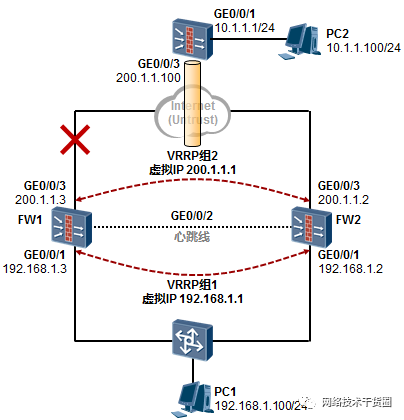
则FW1、FW2将发生主备切换,而此时由于FW2已经拥有了IPSec SAs并且这些SAs与FW1上的是相同的,因此受保护流量可以平滑的切换到FW2上来。
再考虑另外一种情况,就是FW1掉电重启的情况。由于掉电重启,FW1将丢失IPSec SAs,此时FW2成为主设备接替其工作。在FW1启动完成初期,FW2由于仍然是主设备,因此会向FW1 同步IPSec SAs,在FW1抢占了FW2的主设备身份后,即可正常的转发受保护流量。在这里要注意,HRP抢占的时间要设置的合理,不应设置得太短。
注意:
实验中使用的防火墙软件版本为:V300R001C00SPC700。
在完成配置后,FW3会与主防火墙FW1完成IPSecVPN隧道的建立,FW1会将建立好的IPSecSAs同步到备份防火墙FW2上,主备防火墙的IPSec SAs的策略、入站及出站的SPI都是一样的。当FW1发生故障时,FW1/FW2主备切换,受保护流量被引导到备防火墙上,由于此时备防火墙早已有IPSec SAs,因此可以实现平滑的切换。
当PC1主动发起访问PC2的时候,主防火墙FW1/是无法与FW3正确的建立IPSecVPN隧道的,这是因为FW1发送的ISAKMP报文源地址为200.1.1.3也就是FW1的物理接口IP,而在FW3上我们配置的peer地址为200.1.1.1,两者并不匹配,因此IPSecVPN隧道无法正确建立。但是PC2可主动发起访问PC1,这将触发FW3主动与200.1.1.1建立IPSecVPN隧道,这是能够成功的。FW3的ISAKMP报文将发向200.1.1.1,报文实际是发送到主防火墙FW1上,FW1即使未配置local-address,但是FW1(实验版本为V300R001C00SPC700)能够正确处理这些报文并最终正确地完成隧道的建立,虽然如此,仍然建议在FW1、FW2上配置local-address。如果防火墙作为IPSec隧道的发起方,必须执行命令local-address ip-address,设置本端发起协商的地址为VRRP备份组的虚拟IP地址。
双机热备的环境下,只支持主备备份方式的IPSec VPN。
FW1/FW2防火墙的上下行业务接口必须为三层接口(包括VLANIF接口)。
先建立双机热备状态,再配置IPSec VPN。在主用防火墙上配置的IPSec策略会自动备份到备用防火墙上。在备用防火墙上,只需要在出接口上应用备份过来的IPSec策略即可。
审核编辑:郭婷
-
IPSecVPN + PPTP VPN Demo搭建配置说明2024-07-26 605
-
IR915与AF1000建立IPSecVPN配置的过程2024-07-24 701
-
防火墙双机热备命令行配置方案2024-01-02 1976
-
Juniper防火墙IPSec VPN的配置2023-04-03 6391
-
东用科技与华为防火墙构建IPSec VPN配置指导手册2023-03-24 2329
-
发现 STM32 防火墙的安全配置2018-07-27 5415
-
如何配置Cisco PIX防火墙2010-01-13 724
-
防火墙的VPN支持2010-01-08 940
-
[原创]OEM防火墙、OEM SSL VPN、OEM流量控制设备2009-12-02 2416
-
防火墙技术2009-06-16 861
-
基于防火墙钩子的IPSec VPN研究与实现2009-03-24 888
-
防火墙的配置2008-09-24 2654
全部0条评论
快来发表一下你的评论吧 !

