

探讨异常检测技术在网联车辆网络安全
电子说
描述
异常检测技术已经被应用于确保解决网络安全和网联车辆安全性等挑战性问题。本文提出了这个领域的先前研究的分类。本文提出的分类学有3个总体维度,包括9个类别和38个子类别。从调查中得出的主要观察结果是:真实世界的数据集很少被使用,大多数结果来自仿真;V2V / V2I通信和车载通信不一起考虑;提议的技术很少针对基线进行评估;网联车辆的安全没有网络安全那么受关注。
I.介绍
Velosa等人 [1]预测到2020年将有25亿辆网联车辆上路。车联网是指能够连接到网络的车辆,即它可以与其他车辆(V2V)或基础设施(V2I)进行通信,因而可以增强信息娱乐功能以及可以减少碰撞和避免拥塞[2]复杂的等进行复杂功能的应用。在V2V的情况下,通常建议车辆之间形成车辆自组织网络( VANET )。
虽然网联车辆可以增加乘客的便利性以及行驶的安全性,但它们也很容易受到网络攻击[3]。一些研究[4]、[5]、[6]已经发现并证明了普通车辆中可利用的漏洞。网联车辆连接数量的增加会增加这些漏洞的脆弱性的影响和普遍程度。此外,确保网联车辆的安全性变得至关重要,因此各国政府加大了实现功能性VANET的力度[7]。
本文对自2000年初以来的研究进行了调查和分析,即对网联车辆的安全和网络安全问题进行异常检测。异常检测是识别不遵循预期模式[ 8 ]的数据点或事件的过程。据悉,这是第一项在此背景下调查异常检测使用的研究。我们提出了一个基于3个总体类别和9个子类别的分类法。我们还有38个维度来分类所有的调查论文。
我们调查和分析后得出以下推论:
1)大多数研究(65篇调查论文中有37篇)是在仿真数据集上进行的(65篇调查论文中只有19篇使用了真实世界的数据集)。
2)V2X和车载通信基本上没有被一起探索(65个调查论文中的1个除外),这使得研究比较分散。
3)与网络安全相比,网联车辆的安全性(65份调查论文中只有21份)的研究较少。
4)与基线相比,新提出的采用异常检测技术的方法很少(在65份调查论文中只有4篇),导致我们提出的方法的有效性量化较差。
因此,我们建议,应该更加重视建立基准和基线技术,以此来评估新技术。此外,我们还主张更多地利用真实世界的数据,而不是仿真数据。
论文的其余部分组织如下:我们在第II部分和第III部分探讨相关工作和我们的调查方法,并在第Ⅳ部分提出我们的分类法。
II.相关工作
与当前的调查不同,自20世纪初以来,以前的调查分别考虑了VANET和车载网络。例如,outernali等人[ 9 ]调查了VANETs以及Sakiz等人提出的各种入侵检测方法。[10]全面调查了所有可能的攻击,并提出了与VANETs相关的检测机制。这两项研究都没有考虑可能的基于车载网络的网络安全问题。很少有研究调查车载网络中可能存在的威胁和对策。例如Liu等人、McCune等人和Kelberger等人 [11],[12],[13]提出了车载(控制器局域网(CAN),本地互连网络(LIN),FlexRay等)的各种威胁和可能的对策,网络安全问题(基于VANET的问题不是考虑)。我们目前的调查是第一次在网联车辆的背景下审查异常检测技术。
III.调查方法
为了确保可重复性,我们的调查遵循Wholin的滚雪球方法[14]如下。
范围定义:继Chandola等人之后。 [8]我们将异常检测定义为“在不符合预期行为的数据中查找模式”。形成或学习模型,然后监测数据的一致性。
收集初步研究:我们在Google学术中通过关键字搜索确定了一组初始论文。我们这样做是为了避免出版商的偏见。使用的关键词是: "异常检测"、"连接车辆"、" VANET "、" V2I "、" V2V "、"入侵检测"、"不当行为检测"、" CAN总线"、"车内"、"安全"、"安保"。
滚雪球:通过关键词搜索收集的初始集可能并不详尽。因此,我们进行了前后滚雪球式的收集,以收集初始集引用的所有参考文献。然后通过阅读摘要包括或排除论文,然后考虑范围的彻底阅读(从而消除超出我们范围的论文)。这个滚雪球过程被重复进行,直到没有新的相关论文被添加。我们最终研究了有65篇论文。
虽然Wholin [14]建议联系该领域的知名研究人员以获取更多相关文献,但我们忽略了这一步骤,因为鉴于该领域的多样性,我们无法最终确定最重要的研究人员。
数据提取和分类发展:通过Wholin的调查方法[14],一旦详尽地收集了所有相关论文,我们就记下了每篇论文的关键要素。我们使用了一种开放式卡片分类技术[15],收集了关键点,以得出我们提议的分类的维度。开放式卡片分类技术是通过参与者之间的共识将关键元素组织成概念组的过程。我们使用这种技术来达到我们的38个维度(底层)。然后,我们使用自下而上的方法,将这些维度分为9个子类别(中级),我们后来根据排序的多次迭代将其归入3个总体类别(顶级)。我们只在这项研究的作者中进行了公开卡片分类的过程,尽管这个过程通常涉及更大的群体[ 15 ]。最后,我们通过标记将收集到的每篇论文都归入我们的分类体系,通过用它们占据的每个指定维度标记每个论文。
IV.分类
上述过程产生了一个分类法(见图1),包含3个顶级类别,9个子类别和38个维度。这些类别代表了研究领域的更高层次特征。我们的目标是确定每篇论文所针对的威胁、解决方案和研究特征。特别是,抓住了研究特点,对实验的类型和严谨性进行了阐述。
反过来,每个提议的类别包括几个子类别。威胁特征有两个子类别,解决方案特征有4个子类别,研究特征各有3个子类别,可以更好地捕捉每个类别的特征。子类别还具有如图1所示的尺寸,这些尺寸捕捉并突出了区分每个子类别的技术差异,如下所示:
A.威胁特征
这一类别涉及每篇调查论文所涉及的威胁。我们将其划分为两个正交的子类别,如下所示。
1)攻击面:攻击面识别网联车辆中的潜在弱点。例如,一篇论文可能是针对基于CAN总线的攻击(其他总线由于缺乏足够的文献而未被考虑),而其他一些论文则专门关注伪造车辆ECU (电子控制单元)输出的攻击。
2)攻击方法:一篇论文可能涉及不止一种攻击方法。我们特别提请注意此子类别中的黑/灰/虫洞攻击维度。这些是基于路由的攻击,包括丢弃、选择性转发或恶意重新路由VANET[16]中的通信数据包。
B.解决方案特征
这一类别代表了为应对威胁而提议的解决方案的性质。
1)动机:异常检测技术是用于检测威胁还是也提供对威胁的响应?
2)部署点:网联车辆的哪一部分是建议部署的解决方案。例如,可以在车辆的ECU中或在VANET的中央管理机构(CA)或路侧单元(RSU)中部署解决方案。
3)安全目标:是否保护了信息安全(完整性,机密性,可用性)[17]和/或网联车辆的安全性。人身安全不在这项工作的范围之内。
4)异常检测方法:异常可以用多种方式检测。分类法区分了所使用的异常检测方法。我们在这里提请注意基于规则的方法维度,它只代表从车辆操作中自动推断规则的研究,而不是那些从专家那里引出规则的研究。
C.研究特点
虽然上述类别根据已解决的威胁和已确定的维度区分了先前的研究,但这一类别涉及研究方法和数据。
1)科学性:该子类别可记录一篇论文是属于理论论文,实验论文,实证论文还是调查论文。论文可以是类型的组合。
2)数据来源:该子类别记录论文是否使用现实数据或仿真数据。
3)数据集:该子类别记录论文是使用VANET还是车载(CAN总线等)或自然数据[18]。如果一篇论文观察了运行中的连接车辆,并观察了其自然运行环境中的数据,而没有引入任何人工数据(例如,攻击),则认为该论文使用了自然数据。
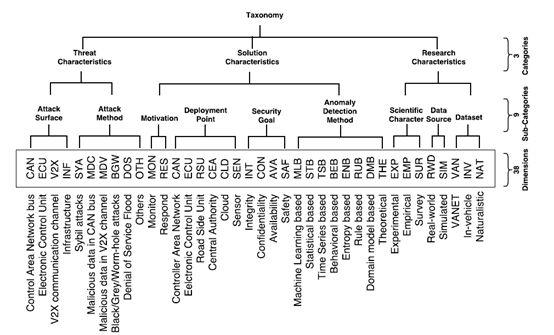
图1.描述所有维度、类别、子类别的分类结构。框中的尺寸首字母缩略词是表I的列标题
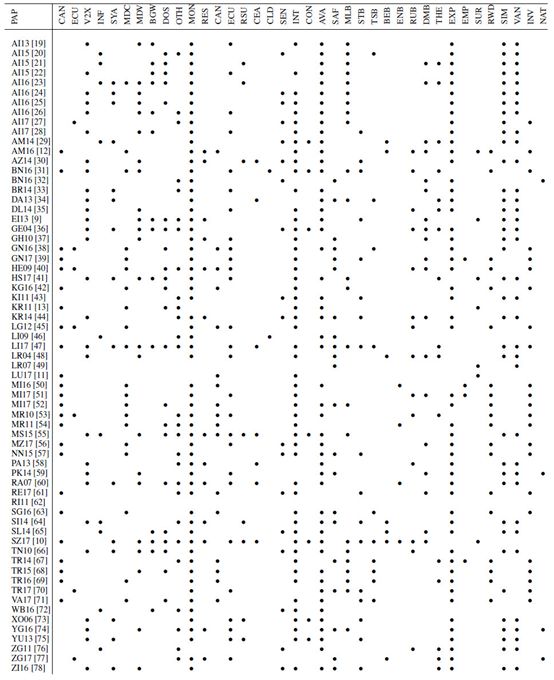
V.从分类法中得出的推论
表I列出了根据第IV节中描述的分类法对第III部分收集的论文进行的分类。以这种方式呈现论文分类的主要目的是从中得出推论和见解,在本文中,我们得出的推论侧重于分析研究现状。表I中的每篇论文在“PAP”栏中用第一个字母和最后一个字母表示第一作者的姓氏和出版年份。
A.关注
我们对调查的分析中发现了两个问题。研究VANET的论文都没有使用真实世界的数据。在我们调查和分类的所有论文中,VANET中甚至没有一篇论文(在研究VANET数据的35/65篇论文中)使用真实数据(所有研究都是在仿真数据集上进行的(37/65篇论文))。我们可以从表I中看到这一点,观察到在研究特征类别中没有VANET和真实世界维度上都有标记的论文。总体而言,在65篇被调查的论文中,只有28篇使用真实世界的数据集(大部分在车载网络研究中)。
我们所提出的基于异常检测的解决方案很少针对基线进行评估。从表I中的经验维度(EMP)可以看出,只有4篇被调查的论文(65篇调查论文中有4篇)评估了针对基线的拟议解决方案。我们预计建立一个量化改进的基线将是一个领域成熟的可喜迹象[79]。
B.差距
这个研究领域还有三个明显的空白有待填补。
除了65篇调查论文中的1篇论文(Levi等[47])外,没有其他论文通过同时分析车载和VANET数据来考虑保护网联车辆:即使来自VANET或车载网络的故障/恶意通信也可能影响网联车辆的安全性。例如,如果网联车辆的车载网络受到危害,则可能开始将故障数据发送到VANET,而VANET又可能危及其他车辆。
与确保网络安全相比,车联网安全性受到的关注较少。在许多情况下,安全漏洞可能危及网联车辆的安全性,反之亦然。因此,即使在没有安全问题的情况下也确保网联车辆的安全性是重要的。只有少数被调查的论文(65篇被调查论文中的13篇)也考虑应对已发现的威胁。大多数论文(65篇调查论文中的59篇)仅用于在异常检测的帮助下监测威胁。
表Ⅰ
显示分类论文分配的矩阵
VI.结论
为了提高连接车辆的安全性,本文对异常检测进行了研究。异常检测研究的广泛使用和零散的发表导致了大量文献的出现,其中存在许多空白和问题。为了找出这些差距和关注点,并对研究领域做了一个全面的了解,我们对65份相关论文进行了调查,在调查期间开发了一种新的分类法,并根据分类法对调查的论文进行了分类,以找出差距。
该调查表明:
大部分研究是在仿真数据上进行的(65份调查论文中有37篇);车载网络数据和VANET数据很少被一起考虑来用于保护网联车辆(65份调查论文中除1份外);
网联车辆安全研究没有得到网络安全研究那么多关注(在65篇调查论文中只有13篇);
而且,许多研究没有对照基线评估提出新的技术(在65篇调查论文中只有4篇这样做),这可能导致难以量化的结果。
因此,我们敦促研究人员解决这些发现的问题,并定期用我们提议的分类学来分析研究,以了解研究的现状及其演变。
REFERENCES
[1] A. Velosa, J. Hines, H. LeHong, and E.Perkins, “Predicts 2015: TheInternet of Things,” Gartner: Stamford, CT, USA,2014.
[2] C. Evans-Pughe, “The connected car,” IEEReview, vol. 51, no. 1, pp.42–46, 2005.
[3] P. Papadimitratos, L. Buttyan, T. Holczer,E. Schoch, J. Freudiger,M. Raya, Z. Ma, F. Kargl, A. Kung, and J.-P. Hubaux,“Securevehicular communication systems: design and architecture,” IEEE
Communications Magazine, vol. 46, no. 11,2008.
[4] S. Checkoway, D. McCoy, B. Kantor, D.Anderson, H. Shacham,S. Savage, K. Koscher, A. Czeskis, F. Roesner, T. Kohno etal.,“Comprehensive experimental analyses of automotive attack surfaces.”
in USENIX Security Symposium. SanFrancisco, 2011.
[5] C. Miller and C. Valasek, “Adventuresin automotive networks andcontrol units,” DEF CON, vol. 21, pp. 260–264, 2013.
[6] R. M. Ishtiaq Roufa, H. Mustafaa, S. O.Travis Taylora, W. Xua,M. Gruteserb, W. Trappeb, and I. Seskarb, “Security andprivacy vulnerabilities of in-car wireless networks: A tire pressure monitoringsystem case study,” in 19th USENIX Security Symposium, Washington DC, 2010, pp.11–13.
[7] U. DoT, “Connected vehicle pilotdeployment program,” 2016. [Online]. Available:https://www.its.dot.gov/pilots/index.htm
[8] V. Chandola, A. Banerjee, and V. Kumar,“Anomaly detection: A survey,” ACM computing surveys (CSUR), vol. 41, no. 3, p.15, 2009.
[9] M. Erritali and B. E. Ouahidi, “Areview and classification of various VANET intrusion detection systems,” in2013 National Security Days (JNS3), 2013, pp. 1–6.
[10] F. Sakiz and S. Sen, “A survey of attacksand detection mechanisms on intelligent transportation systems: VANETs andIoV,” Ad Hoc Networks, vol. 61, pp. 33–50, 2017.
[11] J. Liu, S. Zhang, W. Sun, and Y. Shi, “In-vehiclenetwork attacks and countermeasures: challenges and future directions,” IEEENetwork, vol. 31, no. 5, pp. 50–58, 2017.
[12] S. Abbott-McCune and L. A. Shay,“Intrusion prevention system of automotive network CAN bus,” in 2016 IEEEInternational Carnahan Conference on Security Technology (ICCST), 2016, pp.1–8.
[13] P. Kleberger, T. Olovsson, and E. Jonsson,“Security aspects of the in-vehicle network in the connected car,” in 2011 IEEEIntelligent Vehicles Symposium (IV), 2011, pp. 528–533.
[14] C. Wohlin, “Guidelines for snowballingin systematic literature studies and a replication in software engineering,” inProc. 18th Intl. Conf. on Evaluation and Assessment in Software Engineering,2014, p. 38.
[15] M. Soegaard and R. F. Dam, Theencyclopedia of human-computer interaction. The Interaction Design Foundation,2012, ch. 2.2: Card Sorting.
[16] V. S. Abel, “Survey of attacks on mobileadhoc wireless networks,” International Journal on Computer Science andEngineering, vol. 3, no. 2, pp. 826–829, 2011.
[17] J. Andress, The basics of informationsecurity: understanding the fundamentals of InfoSec in theory and practice.Syngress, 2014.
[18] T. A. Dingus, S. G. Klauer, V. L.Neale, A. Petersen, S. E. Lee, J. Sudweeks, M. Perez, J. Hankey, D. Ramsey, S.Gupta et al., “The 100-car naturalistic driving study, phase II-results of the100-car field experiment,” U.S DoT, Tech. Rep., 2006.
[19] K. M. Alheeti, L. Al-Jobouri, and K. McDonald-Maier,“Increasing the rate of intrusion detection based on a hybrid technique,” in2013 5th Computer Science and Electronic Engineering Conference(CEEC). IEEE, 2013, pp. 179–182.
[20] K. M. Alheeti, A. Gruebler, and K.McDonald-Maier, “An intrusion detection system against malicious attacks on thecommunication network of driverless cars,” in 2015 12th Annual IEEE Consumer Communicationsand Networking Conf. (CCNC), 2015, pp. 916–921.
[21] K. M. Alheeti, A. Gruebler, and K. McDonald-Maier,“On the detection of grey hole and rushing attacks in self-driving vehicular networks,”in 2015 7th Computer Science and Electronic Engineering Conference (CEEC).IEEE, 2015, pp. 231–236.
[22] K. M. Alheeti, A. Gruebler, and K.McDonald-Maier, “An intrusion detection system against black hole attacks onthe communication network of self-driving cars,” in 2015 6th InternationalConference on Emerging Security Technologies (EST). IEEE, 2015, pp. 86–91.
[23] K. M. Alheeti and K. McDonald-Maier,“Hybrid intrusion detection in connected self-driving vehicles,” in 22nd IEEEInternational Conference on Automation and Computing (ICAC), 2016, pp. 456–461.
[24] K. M. Alheeti and K. McDonald-Maier,“An intelligent intrusion detection scheme for self-driving vehicles based onmagnetometer sensors,” in 2016 International Conference for Students on AppliedEngineering (ICSAE). IEEE, 2016, pp. 75–78.
[25] K. M. Alheeti, A. Gruebler, K.McDonald-Maier, and A. Fernando, “Prediction of DoS attacks in external communication for self-drivingvehicles using a fuzzy Petri net model,” in 2016 IEEE International Conferenceon Consumer Electronics (ICCE), 2016, pp. 502–503.
[26] K. M. Alheeti, A. Gruebler, and K.McDonald-Maier, “Intelligent intrusion detection of grey hole and rushingattacks in self-driving vehicular networks,” Computers, vol. 5, no. 3, p. 16,2016.
[27] K. M. Alheeti, R. Al-Zaidi, J. Woods,and K. McDonald-Maier, “An intrusion detection scheme for driverless vehiclesbased gyroscope sensor profiling,” in 2017 IEEE International Conference onConsumer Electronics (ICCE), 2017, pp. 448–449.
[28] K. M. Alheeti, A. Gruebler, and K.McDonald-Maier, “Using discriminant analysis to detect intrusions in externalcommunication for self-driving vehicles,” Digital Communications and Networks,vol. 3, no. 3, pp. 180–187, 2017.
[29] M. Al-Mutaz, L. Malott, and S. Chellappan,“Detecting Sybil attacks in vehicular networks,” Journal of Trust Management,vol. 1, p. 4, 2014.
[30] K. C. Abdelaziz, N. Lagraa, and A.Lakas, “Trust model with delayed verification for message relay in VANETs,” in2014 International Wireless Communications and Mobile Computing Conference (IWCMC).IEEE, 2014, pp. 700–705.
[31] O. Berlin, A. Held, M. Matousek, and F.Kargl, “POSTER: Anomalybased misbehaviour detection in connected car backends,”in 2016 IEEE Vehicular Networking Conference (VNC), 2016, pp. 1–2.
[32] A. R. Beukman, G. P. Hancke, and B. J.Silva, “A multi-sensor system for detection of driver fatigue,” in 14thInternational Conference on Industrial Informatics (INDIN). IEEE, 2016, pp.870–873.
[33] N. Bissmeyer, “Misbehavior detectionand attacker identification in vehicular ad-hoc networks,” PhD Thesis, TUBerlin, 2014.
[34] N. Dutta and S. Chellappan, “A time-seriesclustering approach for Sybil attack detection in vehicular ad hoc networks,”in Proc. Intl. Conf. on Advances in Vehicular Systems, Technologies, andApplications, Nice, 2013, pp. 21–26.
[35] S. Dietzel, R. van der Heijden, H. Decke,and F. Kargl, “A flexible, subjective logic-based framework for misbehaviordetection in V2V networks,” in Proceeding of IEEE International Symposium on aWorld of Wireless, Mobile and Multimedia Networks 2014, 2014, pp. 1–6.
[36] P. Golle, D. Greene, and J. Staddon,“Detecting and correcting malicious data in VANETs,” in Proceedings of the 1stACM International Workshop on Vehicular Ad Hoc Networks. ACM, 2004, pp. 29–37.
[37] M. Ghosh, A. Varghese, A. Gupta, A. A.Kherani, and S. N. Muthaiah, “Detecting misbehaviors in VANET with integrated root-cause analysis,”Ad Hoc Networks, vol. 8, no. 7, pp. 778–790, 2010.
[38] M. Gmiden, M. H. Gmiden, and H.Trabelsi, “An intrusion detection method for securing in-vehicle CAN bus,” in2016 17th International Conference on Sciences and Techniques of AutomaticControl and Computer Engineering (STA). IEEE, 2016, pp. 176–180.
[39] A. Ganesan, J. Rao, and K. Shin,“Exploiting consistency among heterogeneous sensors for vehicle anomalydetection,” SAE, Tech. Rep. 2017-01-1654, 2017.
[40] T. Hoppe, S. Kiltz, and J. Dittmann,“Applying intrusion detection to automotive it-early insights and remainingchallenges,” vol. 4, pp. 226–235, Jan. 2009.
[41] R. E. Haas, D. P. F. Mller, P. Bansal,R. Ghosh, and S. S. Bhat, “Intrusion detection in connected cars,” in 2017 IEEE Intl. Conf. on ElectroInformation Technology (EIT), 2017, pp. 516–519.
[42] M.-J. Kang and J.-W. Kang, “Intrusiondetection system using deep neural network for in-vehicle network security,”PLoS ONE, vol. 11, no. 6, 2016.
[43] B. Khorashadi, F. Liu, D. Ghosal, M.Zhang, and C. N. Chuah, “Distributed automated incident detection with VGRID,”IEEE Wireless Communications, vol. 18, no. 1, pp. 64–73, 2011.
[44] N. Kumar and N. Chilamkurti, “Collaborativetrust aware intelligent intrusion detection in VANETs,” Computers &Electrical Engineering, vol. 40, no. 6, pp. 1981–1996, 2014.
[45] C. Ling and D. Feng, “An algorithm fordetection of malicious messages on CAN buses,” in 2012 National Conference onInformation Technology and Computer Science. Atlantis Press, 2012.
[46] X. Li, Z. Li, J. Han, and J. G. Lee,“Temporal outlier detection in vehicle traffic data,” in 2009 IEEE 25thInternational Conference on Data Engineering, 2009, pp. 1319–1322.
[47] M. Levi, Y. Allouche, and A. Kontorovich,“Advanced analytics for connected cars cyber security,” arXiv:1711.01939 [cs],2017.
[48] T. Leinm¨uller, A. Held, G. Sch¨afer,and A. Wolisz, “Intrusion detection in VANETs,” in In Proceedings of 12th IEEEInternational Conference on Network Protocols (ICNP 2004) Student PosterSession, 2004.
[49] T. Leinm¨uller, E. Schoch, and C.Maihofer, “Security requirements and solution concepts in vehicular ad hoc networks,”in 4th IEEE Conf. on Wireless on Demand Network Systems and Services, 2007, pp.84–91.
[50] M. Marchetti, D. Stabili, A. Guido,and M. Colajanni, “Evaluation of anomaly detection for in-vehicle networksthrough informationtheoretic algorithms,” in 2016 IEEE 2nd International Forumon Research and Technologies for Society and Industry Leveraging a BetterTomorrow (RTSI), 2016, pp. 1–6.
[51] M. Marchetti and D. Stabili, “Anomalydetection of CAN bus messages through analysis of ID sequences,” in IntelligentVehicles Symposium (IV), 2017 IEEE. IEEE, 2017, pp. 1577–1583.
[52] F. Martinelli, F. Mercaldo, V. Nardone,and A. Santone, “Car hacking identification through fuzzy logic algorithms,” in2017 IEEE International Conference on Fuzzy Systems (FUZZ-IEEE), 2017, pp. 1–7.
[53] M. M¨uter, A. Groll, and F. C. Freiling,“A structured approach to anomaly detection for in-vehicle networks,” in 20106th International Conference on Information Assurance and Security, 2010, pp.92–98.
[54] M. M¨uter and N. Asaj, “Entropy-based anomalydetection for invehicle networks,” in 2011 IEEE Intelligent Vehicles Symposium(IV), 2011, pp. 1110–1115.
[55] L. Maglaras, “A novel distributedintrusion detection system for vehicular ad hoc networks,” InternationalJournal of Advanced Computer Science and Applications(IJACSA), vol. 6, 2015.
[56] M. Markovitz and A. Wool, “Fieldclassification, modeling and anomaly detection in unknown CAN bus networks,”Vehicular Communications, vol. 9, pp. 43–52, 2017.
[57] S. N. Narayanan, S. Mittal, and A. Joshi,“Using data analytics to detect anomalous states in vehicles,” arXiv:1512.08048[cs], 2015.
[58] V. L. Praba and A. Ranichitra, “Detectingmalicious vehicles and regulating traffic in VANET using RAODV protocol,”International Journal of Computer Applications, vol. 84, no. 1, 2013.
[59] O. Pattnaik and B. K. Pattanayak,“Security in vehicular ad hoc network based on intrusion detection system,”American Journal of Applied Sciences, vol. 11, no. 2, pp. 337–346, 2014.
[60] M. Raya, P. Papadimitratos, I. Aad, D.Jungels, and J. p Hubaux, “Eviction of misbehaving and faulty nodes in vehicular networks,” IEEEJournal on Selected Areas in Communications, vol. 25, no. 8, pp. 1557–1568,2007.
[61] R. Rieke, M. Seidemann, E. K. Talla,D. Zelle, and B. Seeger, “Behavior analysis for safety and security inautomotive systems,” in 2017 25th Euromicro International Conference on Parallel,Distributed and Network-Based Processing (PDP), 2017, pp. 381–385.
[62] J. Rezgui and S. Cherkaoui, “Detectingfaulty and malicious vehicles using rule-based communications data mining,” in2011 IEEE 36th Conference on Local Computer Networks, 2011, pp.827–834.
[63] H. M. Song, H. R. Kim, and H. K. Kim,“Intrusion detection system based on the analysis of time intervals of CANmessages for invehicle network,” in 2016 International Conference onInformation Networking (ICOIN). IEEE, 2016, pp. 63–68.
[64] H. Sedjelmaci, T. Bouali, and S. M.Senouci, “Detection and prevention from misbehaving intruders in vehicularnetworks,” in 2014 IEEE Global Communications Conference, 2014, pp. 39–44.
[65] H. Sedjelmaci and S. M. Senouci, “A newintrusion detection framework for vehicular networks,” in 2014 IEEEInternational Conference on Communications (ICC), 2014, pp. 538–543.
[66] D. Tian, Y. Wang, G. Lu, and G. Yu, “Avehicular ad hoc networks intrusion detection system based on BUSNet,” in 20102nd International Conference on Future Computer and Communication, vol. 1. IEEE,2010, pp. V1–225–V1–229.
[67] A. Theissler, “Anomaly detection inrecordings from in-vehicle networks,” Big data and applications, p. 23, 2014.
[68] A. Taylor, N. Japkowicz, and S. Leblanc,“Frequency-based anomaly detection for the automotive CAN bus,” in 2015 IEEEWorld Congress on Industrial Control Systems Security (WCICSS), 2015, pp.45–49.
[69] A. Taylor, S. Leblanc, and N.Japkowicz, “Anomaly detection in automobile control network data with longshort-term memory networks,” in 2016 IEEE International Conference on DataScience and Advanced Analytics (DSAA), 2016, pp. 130–139.
[70] A. Theissler, “Detecting known andunknown faults in automotive systems using ensemble-based anomaly detection,”Knowledge-Based Systems, vol. 123, pp. 163–173, 2017.
[71] D. K. Vasistha, “Detecting anomaliesin controller area network for automobiles,” Ph.D. dissertation, Texas A&MUniversity, 2017.
[72] O. A. Wahab, A. Mourad, H. Otrok, andJ. Bentahar, “CEAP: SVMbased intelligent detection model for clusteredvehicular ad hoc networks,” Expert Systems with Applications, vol. 50, pp.40–54, 2016.
[73] B. Xiao, B. Yu, and C. Gao, “Detectionand localization of Sybil nodes in VANETs,” in Proceedings of the 2006 Workshopon Dependability Issues in Wireless Ad Hoc Networks and Sensor Networks. ACM, 2006,pp. 1–8.
[74] S. Yang, Z. Liu, J. Li, S. Wang, andF. Yang, “Anomaly detection for Internet of Vehicles: A trust management schemewith affinity propagation,” Mobile Information Systems, vol. 2016, pp. 1–10,2016.
[75] B. Yu, C.-Z. Xu, and B. Xiao, “DetectingSybil attacks in VANETs,” Journal of Parallel and Distributed Computing, vol.73, no. 6, pp. 746–756, 2013.
[76] Y. Zhang and G. Cao, “V-PADA: Vehicle-platoon-awaredata access in VANETs,” IEEE Transactions on Vehicular Technology, vol. 60, no.5, pp. 2326–2339, 2011.
[77] M. Zhang, C. Chen, T. Wo, T. Xie, M.Z. A. Bhuiyan, and X. Lin, “SafeDrive: online driving anomaly detection from large-scale vehicledata,” IEEE Transactions on Industrial Informatics, vol. 13, no. 4, pp. 2087–2096,2017.
[78] K. Zaidi, M. B. Milojevic, V.Rakocevic, A. Nallanathan, and M. Rajarajan, “Host-based intrusiondetection for vanets: A statistical approach to rogue node detection,” IEEETransactions on Vehicular Technology, vol. 65, no. 8, pp. 6703–6714, 2016.
[79]S. Lessmann, B. Baesens, C. Mues, and S. Pietsch, “Benchmarking classificationmodels for software defect prediction: A proposed framework and novelfindings,” IEEE Transactions on Software Engineering, vol. 34, no. 4, pp.485–496, 2008.
-
专家解读 | NIST网络安全框架(1):框架概览2024-05-06 2810
-
汽车网络安全 ISO/SAE 21434是什么?(一)2026-04-07 686
-
汽车网络安全合规全流程深度解析——从法规门槛到落地实践2026-04-21 363
-
汽车网络安全TARA分析全指南:从基础原理到落地实操2026-04-27 206
-
网络安全隐患的分析2012-10-25 2947
-
2020 年网络安全的四大变化2020-02-07 4058
-
定位技术在网络安全领域中的应用是什么2021-05-28 2369
-
在网络安全领域,NIST框架是什么?2023-04-17 911
-
网络安全检测与监控技术的研究2010-12-25 795
-
探讨2019年的网络安全重要趋势2019-01-19 5407
-
入侵检测技术在网络安全中有什么样的应用2020-05-27 1333
-
如何保障智能网联汽车在网络环境下的安全性?2020-07-23 1478
-
人工智能在网络安全中的优势及实施风险2022-10-21 3648
-
从防御视角探讨ChatGPT对网络安全的影响2023-02-23 2256
-
IBM和微软加强在网络安全领域的合作2024-07-10 1553
全部0条评论
快来发表一下你的评论吧 !

